In this Cisco CCNA tutorial, you’ll learn about Cisco’s multi-chassis EtherChannel options of StackWise, vPC, and VSS. Scroll down for the video and also text tutorial.
Cisco StackWise, VSS, and vPC Video Tutorial
Lee Mezzullo

Hello Neil, just wanted to say thank you for your guidance, knowledge and inspiration. Much appreciated. Finally got the CCNA, I passed in my first attempt after taking your awesome class.
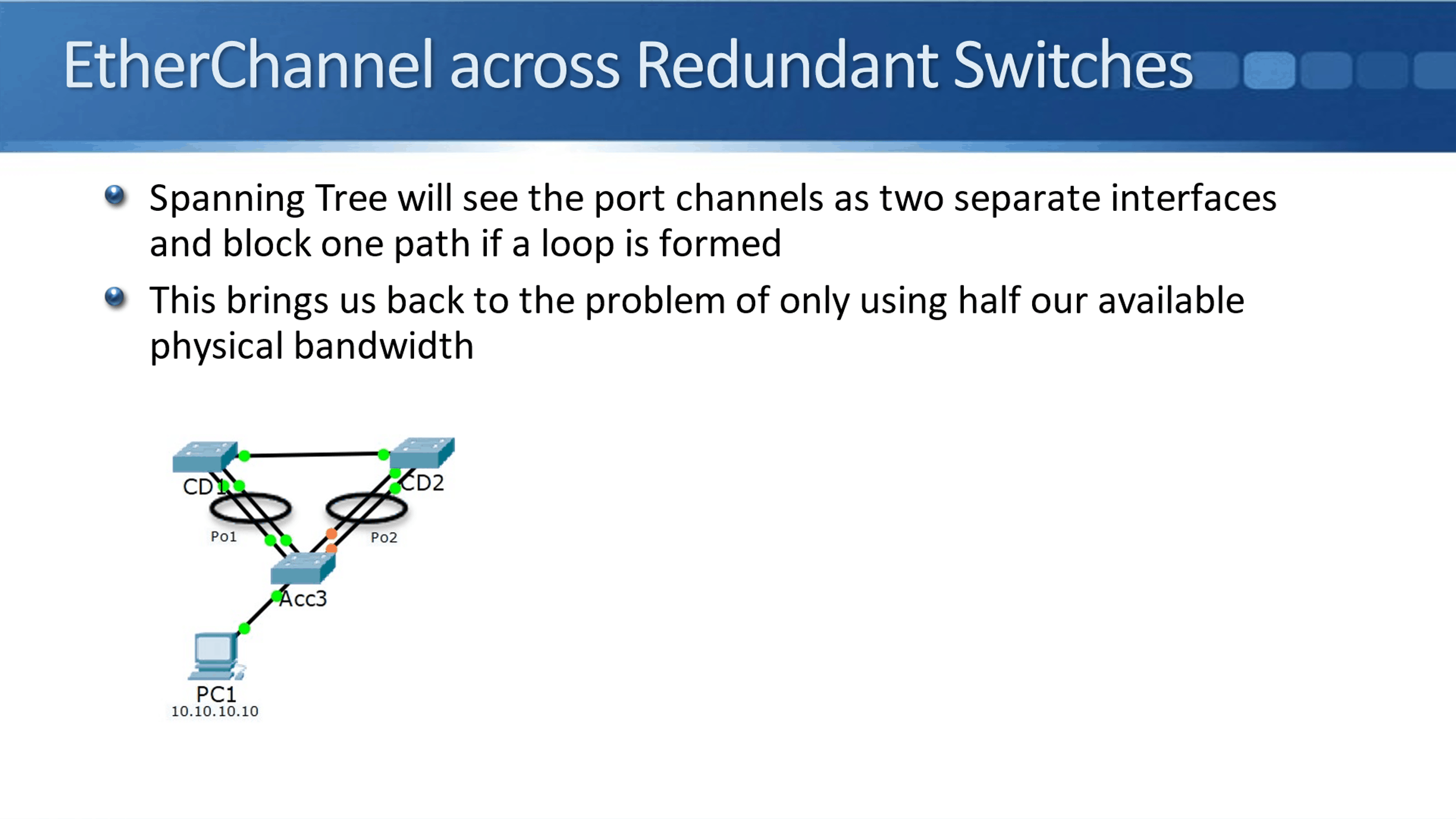
EtherChannel Across Redundant Switches
Matching EtherChannel settings have to be configured on the switches on both sides of the link. You can configure separate port channels from a switch to redundant, upstream switches like you see in the diagram below.
I've got my access layer, Acc3 switch, and it has got a port channel with bundled links going up to CD1. It's got another separate port channel with other physical interfaces that are bundled and a port channel going up to CD2.
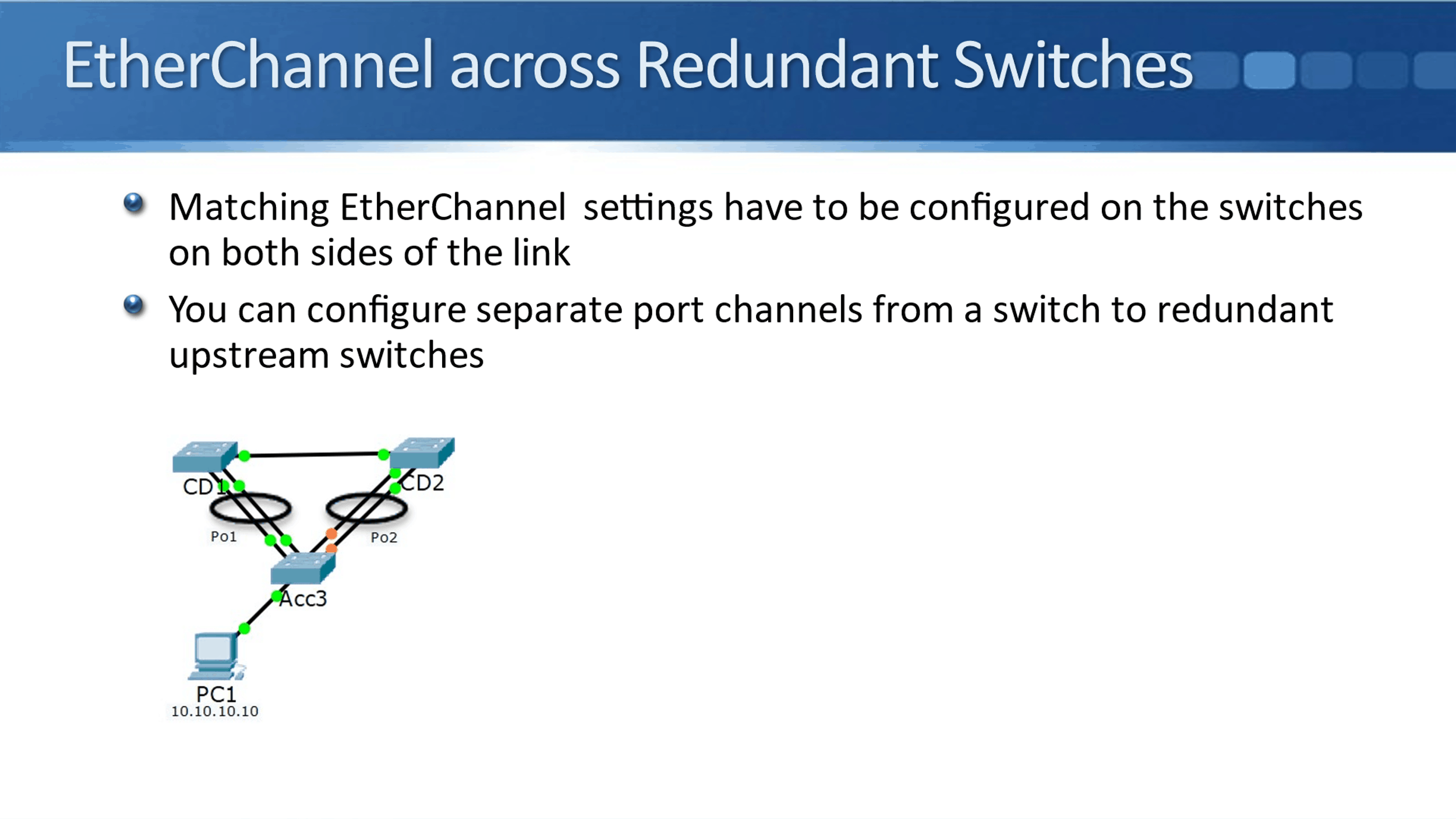
The problem with this is that Spanning Tree will see those separate port channels as two separate interfaces, and it'll block one path if a loop is formed. In our example, CD1 is the root bridge. So, the port channel from Access 3 to that is going to be forwarding, but the port channel going up to CD2 would form a potential loop. Spanning Tree is going to block that port channel.
I've got four physical interfaces configured as uplinks here, but only two of them are forwarding. I'm only getting half of my possible bandwidth, hence, that brings us back to the same problem of only using half of our available physical bandwidth again.
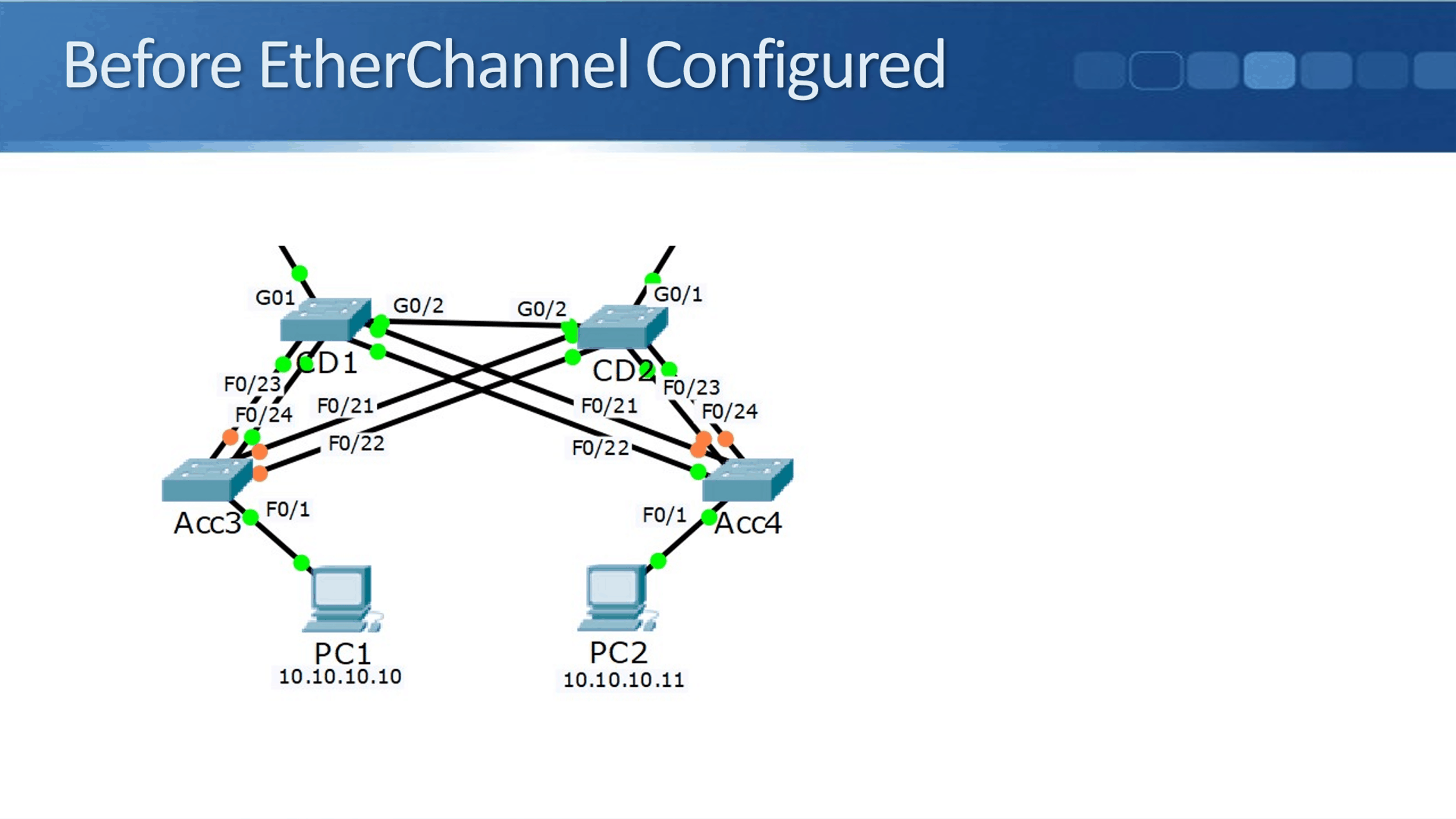
Before EtherChannel Configured
Before configuring EtherChannel in this topology, CD1 is the root bridge. From Acc3, it got those four physical uplinks, but only one of them was forwarding traffic which was the interface connected to CD1. It is the same on Acc4 as well. With the four physical ports, only one of them is forwarding traffic.
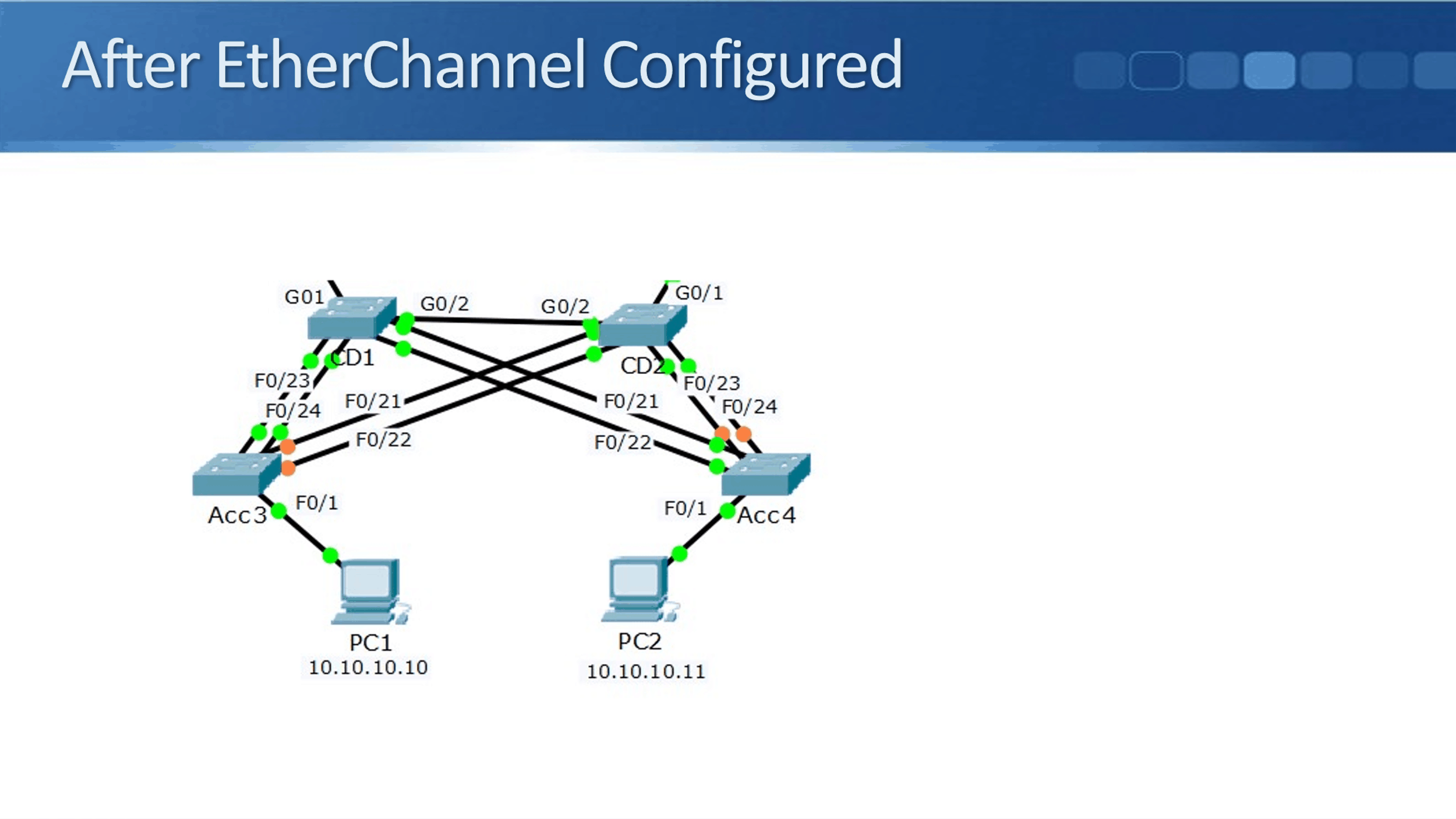
After EtherChannel Configured
After we configured EtherChannel, we have two out of the four forwarding traffic now, rather than one. It's better. I'll go on to Acc3 and do a ‘show etherchannel summary’, you can see that there are two port channels. One is going up to the CD1 switch, the second one is going up to the CD2 switch and they're both up.
When I do a ‘show spanning-tree vlan 10’, which is the VLAN that my PC's are in, I can see that out of those two port channels, one of them is forwarding traffic. This is the port channel connected to the root bridge. The other one is blocking because it's forming a potential loop. So, it’s still not perfect.
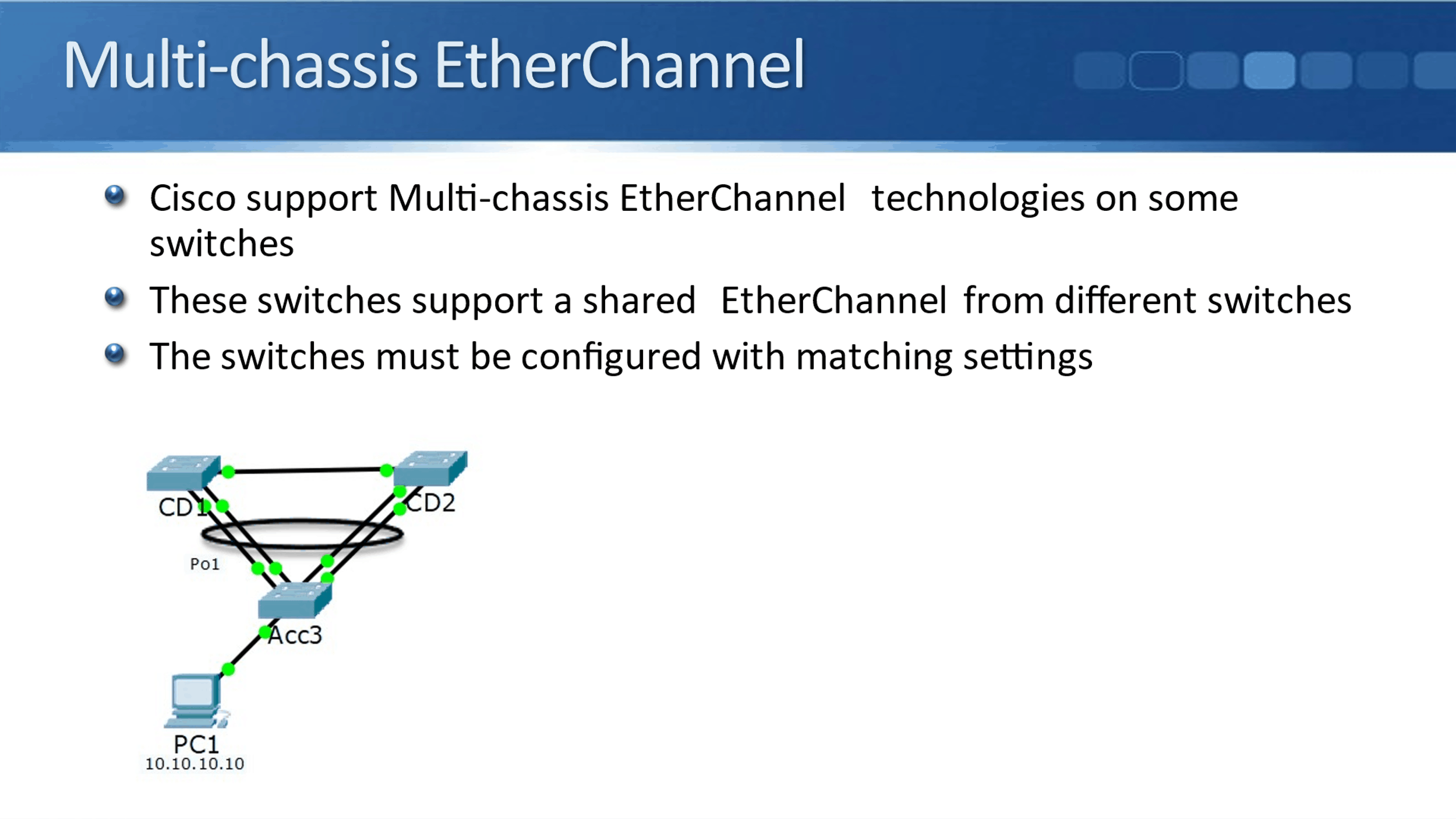
Multi-Chassis EtherChannel
There is a way that we can get this configured so that we are actually forwarding on all of our physically connected uplinks. The way that we do that is with Multi-chassis EtherChannel, which some switches will support.
When we configure it, the switches support a shared EtherChannel from different switches, just like in the diagram below. Normally we would have two separate port channels. One going up to CD1 and another one going up to CD2. When those core distribution layer switches support Multi-chassis EtherChannel though, I can do a single port channel, which goes to both of them.
Now, again, the switches must be configured with matching settings. When you configure EtherChannel, you need matching settings on both sides of the links. In our example, Acc3 has got a port channel going upstream, and switches, CD1 and CD2, have got a shared port channel going downstream.
CD1 and CD2 need to be advanced level switches and they must support talking to each other and having a shared port channel going downstream. This is supported on some models of Cisco switches.
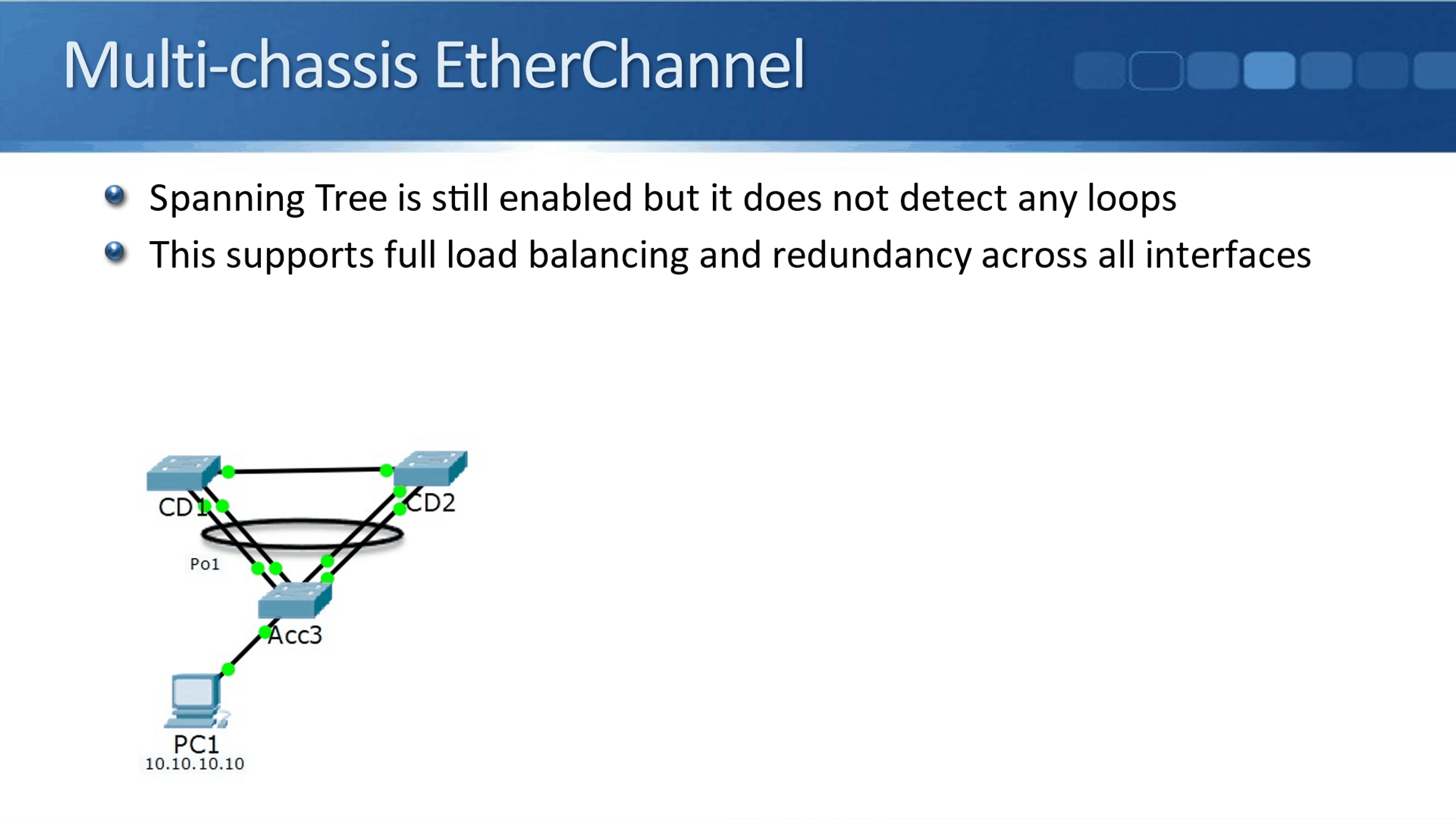
When you do configure this, Spanning Tree is still enabled, but it only sees a single logical interface on both sides. It sees a port channel going upstream from Acc3, and it sees a single port channel going downstream from CD1, and shared with CD2.
Since it sees a single link, so there will be no loop there. Therefore, Spanning Tree does not block any of the ports. We have all of them forwarding. We get the full use of all of our physical bandwidth and it supports full load balancing and redundancy across all the interfaces. If any of the interfaces goes down, it will failover to another available interface.
StackWise, VSS, and vPC
The available Cisco technologies that support this are StackWise, VSS, and vPC. Now, a single switch is not going to support all three of these. Different platforms of switches support different options, and if a switch does support one, it will only be one.
The switch will either support StackWise, or it will support VSS, or it will support vPC, not two or three at the same time. This is only supported on the higher-end switches. If you got one of Cisco's lower-end switches, then this is not going to be supported.
So which option is supported on which family of switches? Well, StackWise is on Catalyst switch platforms, including the Catalyst 3750, 3850, and 9000. Notice I'm just saying "including" here because Cisco comes out with new models of switches very regularly, and when we do come out with a new model of switch, it's likely to support one of these three options. Thus, this will be updated over time.
If you have to look at the picture below, this is a stack of switches that have been configured with StackWise. StackWise uses special proprietary cables at the back of the switches. When you do configure a StackWise stack, the separate physical switches all operate as if they're one switch and they're configured as if they're one switch as well.
That is similar to the next option, which is VSS, the Virtual Switching System. It is supported on the Catalyst 4500 and 6500 switch families.
The last option is one of its own, a little bit different, is vPC or virtual Port Channel. That's supported on the Nexus switches and rather than stacking the switches together and them being managed as if they're a single switch.
When you use this on the Nexus, they're still configured as two separate switches, but you do a matching configuration on them, and that allows for a shared part channel from those switches.
At the CCNA exam level, Cisco expects you to know a broad overview of them, but they don't expect you to know how to configure these. If you go on to the CCNP level or one of the other CCNA tracks, like data center, you'll learn then how to configure and monitor these technologies.
Additional Resources
Configuring Virtual Switching Systems: https://www.cisco.com/en/US/docs/general/Test/dwerblo/broken_guide/vss.html
Configuring Cisco StackWise Virtual: https://www.cisco.com/c/en/us/td/docs/switches/lan/catalyst9600/software/release/16-12/configuration_guide/ha/b_1612_ha_9600_cg/configuring_cisco_stackwise_virtual.html
Multichassis EtherChannel (MEC): https://www.oreilly.com/library/view/network-warrior-2nd/9781449307974/ch07s03.html
Libby Teofilo

Text by Libby Teofilo, Technical Writer at www.flackbox.com
Libby’s passion for technology drives her to constantly learn and share her insights. When she’s not immersed in the tech world, she’s either lost in a good book with a cup of coffee or out exploring on her next adventure. Always curious, always inspired.