In this Cisco CCNA training tutorial, you’ll learn about the private address ranges. Scroll down for the video and also text tutorial.
Private IP Addresses (RFC 1918) Video Tutorial
Simon Rose

I passed the 200-301 CCNA exam last week, 891/1000. I was using your CCNA course so I just wanted to say a big thank you!
These were documented by the Internet Engineering Task Force (IETF) in RFC 1918. RFC stands for Requests For Comments. When the IETF release some documentation, they release it as an RFC number.
Meaning, the other engineers can comment and suggest some improvements but, the RFC is still a finished standard as well. As of today, RFC 1918 is the final standard for private IP addressing.
Sticking with our theme of “how the Internet was originally designed to work”, private IP addresses were originally for hosts that should not be connected to the Internet.
If you're in an organization and you've got a part of your network that you don't want to be connected to the Internet, you should not be paying for public IP addresses for those hosts. That would be a waste of money paying for IP addresses that are never going to be used. You could save money by using private IP addresses instead.
Another benefit you can get is that the hosts are not going to be connected to the Internet, so it makes it more secure and it locks down that they can't talk on the Internet.
Why would anybody ever do that? Maybe it's a highly secured environment, like a bank and the bank has got a part of their network that they want to keep completely off the Internet for security reasons, so they would use private IP addresses there.
Another possible example is in high school and they've got PCs there. The school authorities don't want the kids to be able to get on the Internet. Again, they would use private IP addresses there.
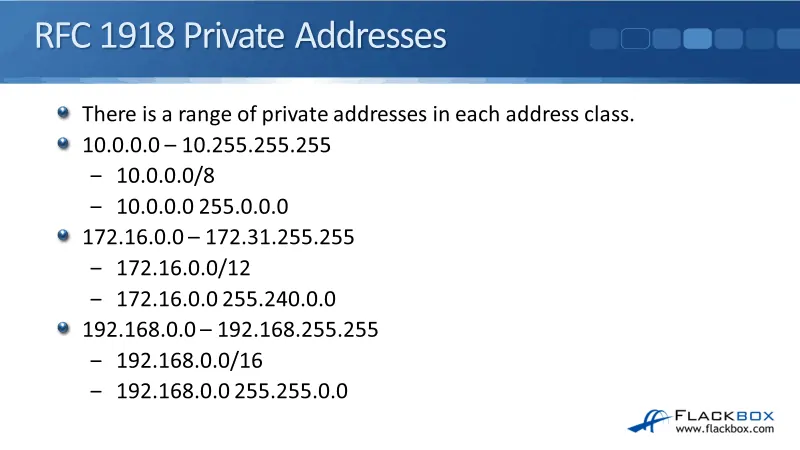
The range of private addresses in each of the different Classes, A, B, and C:
- Class A - 10.0.0.0 to 10.255.255.255
- 10.0.0.0 /8
- 10.0.0.0 255.0.0.0.
- Class B - 172.16.0.0 to 172.31.255.255
- 172.16.0.0 /12
- 172.16.0.0 255.240.0.0
- Class C - 192.168.0.0 to 192.168.255.255
- 192.168.0.0 /16
- 192.168.0.0 255.255.0.0
This is not just for the CCNA exam review. You're expected to know this off the top of your head when you're working because you'll see the RFC 1918 addresses are used a lot in the real world.
RFC 1918 Example 1
Let's look at an example of where we would use private addresses when we wanted to keep our host off of the Internet. This is a secure environment, we've got Bank A on the left and Bank B on the right.
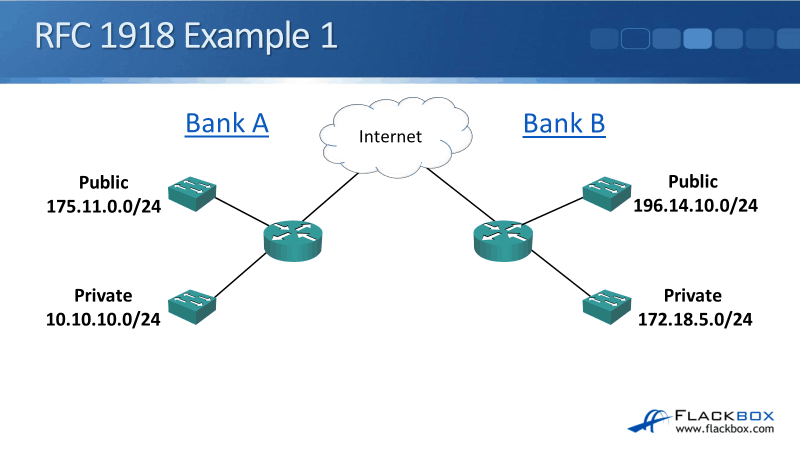
Bank A has got a public part of their network, 175.11.0.0/24, that is used by the staff who are allowed to access the Internet. They've also got a private part of their network, 10.10.10.0, where they have some very sensitive servers that they want to keep off the Internet. Bank B has its public address at 196.14.10.0 and they've also got a private range at 172.18.5.0/24.
RFC 1918 Example 2
In this example, you can see that Bank A and Bank B are both using 192.168.10.0 /24. That's fine. They don't have any connectivity to each other anyway because they're on completely separate networks.
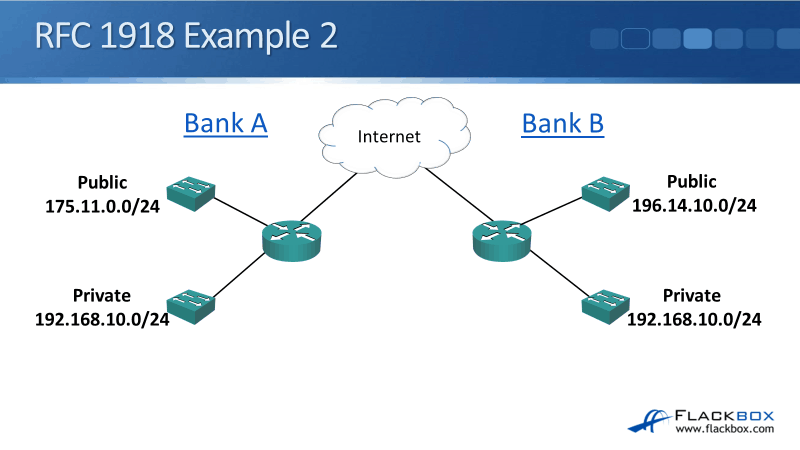
You'll find that with private addresses, loads of organizations all over the world will be using the same private address ranges. However, they can't use the same public address ranges because they need to have connectivity to each other over the Internet.
Private addresses don't have any connectivity outside the organization, so those addresses can be reused over and over again.
The IPv4 Global Address Space Problem
The IPv4 global address space problem began when the designers of IPv4 did not realize how big the Internet was going to get. When they first designed the IPv4 format, they thought that 4.3 billion addresses are going to be more than enough for what would be required. Today, the 4.3 billion is nowhere near enough.
Another problem is that the protocol is not efficient in the way that it allocates addresses. Again, because they thought that they had more than enough addresses, they didn't worry about wasting addresses.
For example, the 127.0.0.0 address, an entire Class A range is wasted just for loopback testing. Moreover, large address blocks were given out to organizations that were not utilizing the actual addresses. The IPv4 address space is not big enough to accommodate the addresses that we need on the Internet today.
IPv6
Quite a while ago, back in the late 1980s, they realized that they were going to run out of addresses. So they started working on a solution to the problem and in the 1990s, the IPv6 was developed.
The addresses we've been talking about up to this point have been IPv4. IPv6 addresses have got a different format:
- IPv4 - 32 bits long
- IPv6 - 128 bits long
The address space is not just four times as big as the IPv4. It's exponentially bigger because we keep doubling it every time we add a bit. The IPv6 address space is 7.9 times 10 to the power of 28 times as many addresses as IPv4.
IPv6 has a huge amount of addresses and it was developed in such a way that they should never run out of addresses again.
The IPv6 Problem and NAT
The main issue with IPv6 is that there's not a seamless migration path from IPv4. So if you're in an organization, you've already got IPv4 addresses running and you've done all of your IPv4 addressing design, it's not easy.
You can't just flick a switch and convert IPv4 to IPv6 because the address format is completely different. IPv6 is not seamlessly backward compatible with IPv4.
It is quite a big project to migrate from IPv4 to IPv6 if you're already an existing organization. Because of that, Network Address Translation (NAT), was implemented temporarily to stop the gap before everybody could convert to IPv6.
Organizations can use RFC 1918 private IP addresses on their inside network, which are not publicly routable, so they won't work on the public Internet. What they can do with those private addresses is that they can convert them to the public IP address on the outside.
So if you're using a private IP address on the inside, whenever you communicate with anybody out on the public Internet, the traffic would look like it's coming from a public IP address. Therefore, they will be able to send the traffic back to you.
Even with many hosts on the inside using private IP addresses, they can share a few or even just a single public IP address on the outside.
Private Addresses and NAT
In our example below, we've got Office A on the left. They've bought a small range of public IP addresses, 175.11.0.1/28, which gives them 14 addresses.
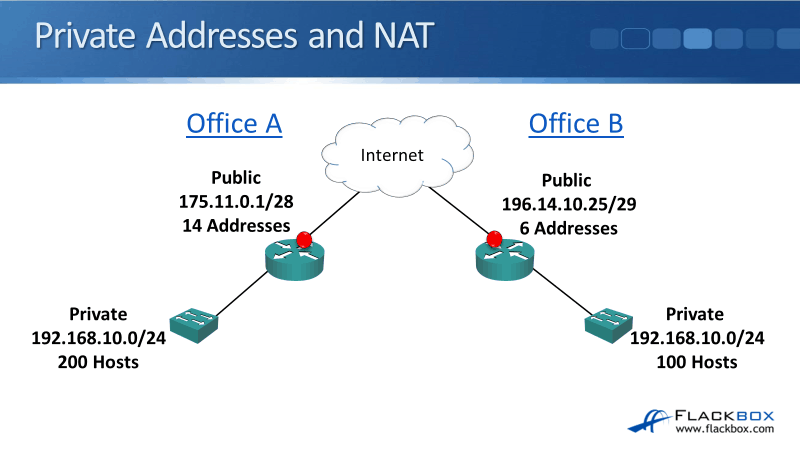
They're using private addresses, 192.168.10.0/24, with 200 hosts on the inside. They're able to convert those private addresses on the inside to the pubic addresses on the outside whenever they communicate with anybody on the Internet.
If we didn't have private addresses, they would have required 200 public IP addresses for those hosts on the inside. With NAT, they're doing it with just 14, and they could've done it with just one if they wanted to.
This saves loads of addresses in the IPv4 public address space. It also saves organizations money as well because they don't need to pay for those public IP addresses.
Today’s Networks
Let's talk about how things are done most commonly today. Back in the early 2000s, a lot of industry experts predicted that everybody would be using IPv6 within a few years because of the shortage of IPv4 advances.
In today's networks, more enterprises are using RFC 1918 IPv4 addresses with NAT. If you work for a company, the chances are you're going to use private IP addresses on all your inside hosts, and you're translating them to the public IP address on the outside when they go out to the Internet.
The reasons for this are RFC 1918 has a security benefit of hiding your inside hosts by default because those private IP addresses are not routable on the Internet. If you send traffic to a private IP address and it gets out to the Internet, the Internet router is just going to drop that traffic.
Your private IP addresses can route between your hosts on the inside network. You can also route between your hosts over your wide area network, but you cannot send traffic to a private IP address on the Internet.
All of the different companies are using those private IP addresses, the Internet would not know which one to send it to, so therefore it is for internal use within the organization only.
Another reason that there's been a slower-than-expected uptake of IPv6 is that the format is completely different. All of the network engineers that are around today are very comfortable with IPv4. They're used to working with it day in and day out. A lot of them are not comfortable with working with IPv6 because their organization isn't using it yet.
So if you go and speak to one of these engineers and say, "Hey, we need to convert to IPv6." They're probably not going to be too keen on the idea because it's something completely new for them. They're already comfortable with IPv4.
They can give you the answer, "Well, we're already using private addresses in NAT, and it's not causing any issues. Everything's working just fine. So why put all the time, effort, and money into converting IPv6?" So that's why it's been slower for everybody on the Internet to move over to IPv6 than was originally expected.
IPv6 is still found in a lot of places, mostly in services provider networks. The majority of service provider networks support both IPv4 and IPv6. You'll also see it being used for mobile services, like on your mobile phone. This is because there are lots of mobile phones and they're a relatively newer technology.
IPv6 was already out and there was already a shortage of IPv4 addresses. So for mobile services, we are mostly on IPv6. Where you'll also see it is in larger countries that had a later adoption of the Internet, such as India and China.
Spare public IPv4 addresses were exhausted in 2011, so IPv6 is still the future path. You see that most companies today are using the RFC 1918 addresses and NAT but it will slowly move over to IPv6.
You still need to understand subnetting. So don't think, "Oh, well, if we don't have that IPv4 address space problem, why did I have to spend all that time in this section learning about subnetting?"
You're still going to do subnetting even when you're using private IP addresses on the inside because you still need to do your logical addressing. You also need to be able to understand and troubleshoot IP. Everything that you have learned in this section is very applicable to the real world and also of course for passing your CCNA exam.
Because we have the entire private IP address space to work with, it's common to see today's real-world enterprises using /24 subnets for their end hosts, a /30 for their point-to-point link, and a /32 for the loopbacks.
Complex VLSM is where we've got one subnet and we're diving it up into smaller subnets with different-size subnet masks. It's quite complicated when you do that because you have to think, ”Okay, well, where does the actual network portion of the address begin and end?” “What's the broadcast address?”
If you're using a /24, you just look at it and you know that up to the end of the third octet is the network address and the fourth octet is the host address. When we're using private addresses on the inside, we don't have the problem with a lack of IP addresses.
We can use the entire private address space. It's very common to use a /24 just because it's the easiest thing to do and easy is good because it makes fewer mistakes and it makes troubleshooting easier.
Where you will see VLSM being used is if an organization is using public IP addresses on the inside, which does sometimes still happen, and they need to maximize the use of their public IP address. They don't want to waste any because they're paying for them. Then you might see more complex VLSM being used in that kind of scenario.
Contiguous Address and Route Summarization
When you are using private addresses on the inside, as you see in the example below, you're still going to want to do route summarization. It is going to compartmentalize the different parts of your network.
From one part of your network to a different part of your network, you're only going to send a summary address rather than every single route. For example, we've got Region A on the left, and it's using 10.0.0.0 /24, 10.0.1.0 /24, up to 10.0.255.0 /24.
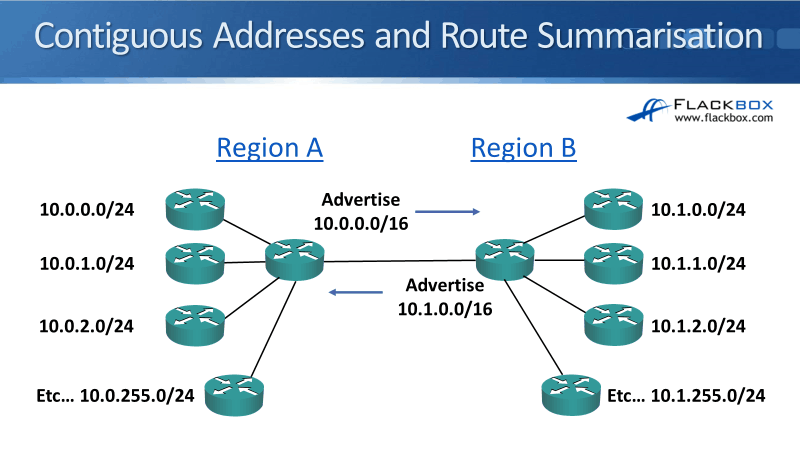
Region B, within the same organization on the right, is using 10.1.0.0 /24, 10.1.1.0 /24, and so on. We then connect the two routers between Region A and Region B. From Region A, we can advertise 10.0.0.0/16 and from Region B, we advertise 10.1.0.0/16.
Rather than advertising all 256 routes in both directions, we only advertise one route. So it takes up less memory on the routers because we've got less routes. If a problem arises, the impact stays local to that particular region.
To be able to do this, you need to be careful with the way that you plan your network addressing. You need to make sure that you allocate them in contiguous blocks like in our example above.
Non-Contiguous Addresses
A mistake in network addressing would be doing it similarly in our example below. On the left, I've got 10.0.0.0 /24, 10.1.0.0 /24, 10.0.2.0 /24, and then 10.1.3.0 /24. On the right, I've got 10.1.0.0 /24, 10.0.1.0 /24, 10.1.2.0 /24, and 10.0.3.0 /24.
I'm mixing up my 10.0.0.0 and my 10.1.0.0. Because of this, I can't advertise 10.0.0.0 from left to right because some of the 10.0.0.0 networks are already on the right.
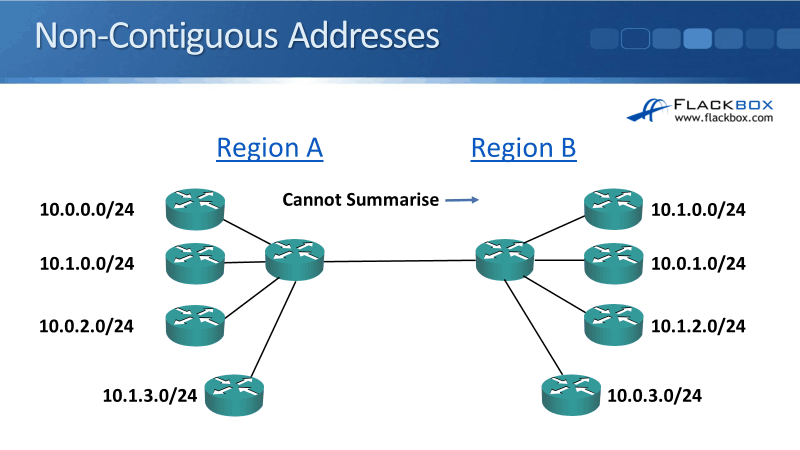
If you made a mistake with your network address planning, you would need to advertise all of the routes everywhere. That's going to end up taking a lot more resources in your routers and it's going to make the network a lot less stable and harder to troubleshoot.
Be careful when you're doing your network addressing design and carefully plan it out at the start. Also, make sure that your addressing is done in contiguous blocks so that you can do your summarization.
Additional Resources
Address Allocation for Private Internets: https://www.cisco.com/c/en/us/support/docs/ip/ip-multicast/13789-35.html
Address Allocation for Private Internets: https://tools.ietf.org/html/rfc1918
Cisco CCNA Routing and Switching 200-120 Exam Cram: Concepts in IP Addressing: https://www.pearsonitcertification.com/articles/article.aspx?p=2169746&seqNum=4
Subnetting Practice Questions: https://www.flackbox.com/subnetting-practice-questions
Libby Teofilo

Text by Libby Teofilo, Technical Writer at www.flackbox.com
Libby’s passion for technology drives her to constantly learn and share her insights. When she’s not immersed in the tech world, she’s either lost in a good book with a cup of coffee or out exploring on her next adventure. Always curious, always inspired.