In this Cisco CCNA training tutorial, you’ll learn about the IP address classes. We’re going to cover Classes A, B, and C which are used for allocating addresses to our hosts, and then Classes D and E. Scroll down for the video and text tutorials.
IP Adress Classes Video Tutorial
John Salmon

I kept hearing how getting your CCNA would change your life. Well it’s true.
I “Crushed” the CCNA exam and went from working as a mail courier to getting my first tech job as a network lab engineer working for Cisco.
Neil’s courses were a critical factor in this. The way he structured the course and provided labs for each section really made it easier to absorb the information. I still go back and watch sections when I am setting up a new lab at work.
Thank you so much for the awesome video courses.
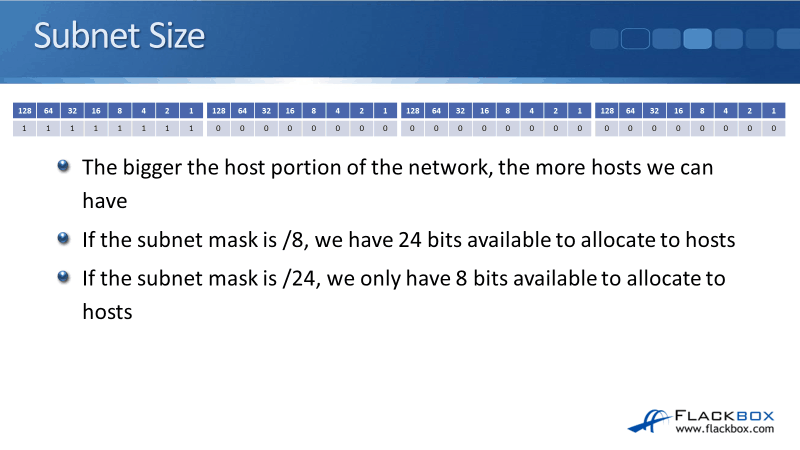
Subnet Size
The first thing to talk about is the line that designates where the network portion and the host portion of the address. If a subnet mask is a /8 for example, we’re going to have 8 bits for the network portion and 24 bits for the host portion.
Comparing that with a /24, we're going to have 24 bits for the network portion and 8 bits for the host portion. With /8, we’re going to have few networks, but a lot of hosts per network. With /24 we'd have a lot of networks, but few hosts per network.
How Internet Addressing Was Meant to Work
Let's talk about how Internet addressing was originally supposed to work. When IPv4 was first conceived, the designers didn't realize that there would be a huge explosion of IP address usage. Everybody would be using and would require an IP address.
IP addressing was designed for what was right at that time. As we go through this tutorial, you need to think about the Internet about how it was then to understand why IPv4 was designed the way that it is.
There are a few issues with IPv4 that you'll learn about and those issues came about because the designers didn't realize what was going to happen in the future. So as long as you think about it from that point of view, then everything should make sense.
The original way that IPv4 addressing was meant to work is that when a company wanted to communicate on the Internet, they would apply for a range of IP addresses. The global assignment of IP addresses is handled by IANA, which stands for the Internet Assigned Numbers Authority.
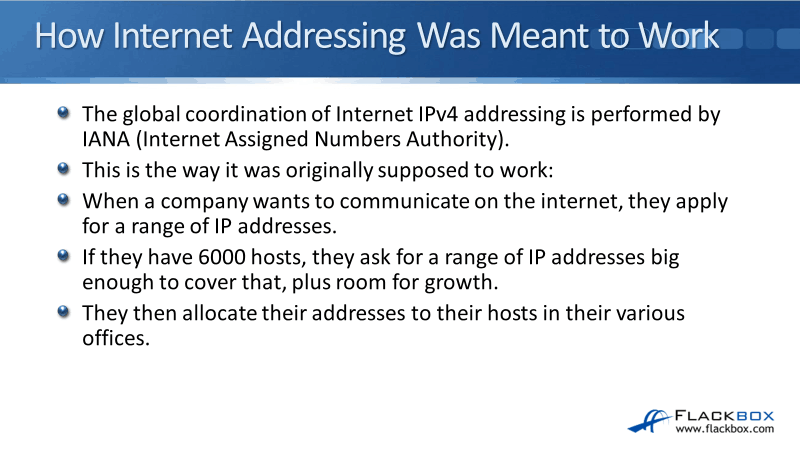
From a global point of view, IANA is at the top level and they assign large blocks of addresses to the local authorities in different regions. Companies would apply to their local authority to get a range of public IP addresses.
If a company has 6000 hosts, for example, they would ask for a range of IP addresses big enough to cover that, plus some room for growth in the future as well. That company would then allocate those addresses to their hosts in their different offices.
Unfortunately, when IPv4 was created, the designers didn't realize how big the Internet was going to get, so they didn't create a big address space. IPv4 addresses are not enough for every host that needs an address that's going to be communicating on the Internet. So, IPv4 ran out of addresses.
The longterm solution for the problem is IPv6, which has got a much bigger address space.
- IPv4 - 32-bit address
- IPv6 - 128-bit address
As a workaround, Private IP addresses with Network Address Translation (NAT) are currently deployed in the majority of enterprise networks. IPv6 is a longterm solution, but nowadays, private address with NAT is more commonly deployed.
Class A
The Internet authorities split the global IPv4 address space into separate classes. Class A addresses are assigned to networks with a very large number of hosts. Class A was going to be a small network portion with a large host portion.
The high-order bit, which is the first bit in a Class A address, is always set to zero. In the figure below, you will see on the left side in the first octet, the first bit was highlighted and it's always going to be a zero in a Class A address.
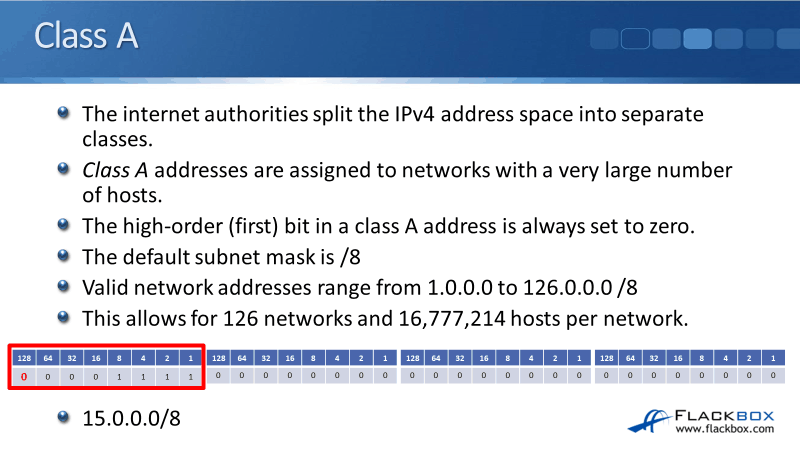
With Class A addresses, the default subnet mask is a /8, which is 255.0.0.0 in the dotted decimal notation. The network address range from 1.0.0.0 to 126.0.0.0/8. The usable host address ranges from 1.0.0.1 to 126.255.255.254. It allows for 126 networks and with the host bits 24 to the power of two, adds up to 16,777,214 hosts per network.
Reserved Class A Addresses
You maybe noticed that if you set the first bit to zero, we would have all zeros 0.0.0.0/8, and we could go up to 127.0.0.0/8. However, all zeros and 127.0.0.0/8 are not included in the valid address range. We can’t assign them to our hosts because they are reserved addresses. 0.0.0.0/8 is reserved and it signifies this network, also, it is used by some protocols.
The range 0.0.0.1 to 0.255.255.255 are not valid addresses that you can assign to hosts. Same with 127.0.0.0/8 which is reserved and used as the loopback address. It is used for testing the IP stack on the local computer. Therefore, the range 127.0.0.1 to 127.255.255.255 are not valid host addresses.
In the figure below, you can see that they just wiped out over 33 million addresses that could've been used for addressing actual hosts on the public Internet. If you think about it, they could've just used a single address to signify ‘this network’ rather than using 16 million addresses.
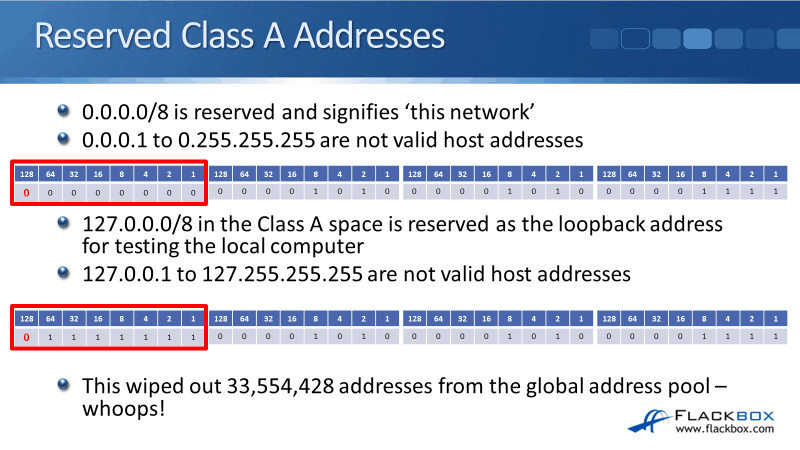
Same for the loopback, they didn't need 16 million addresses to be used for loopback testing. You might be thinking, "Well, there's this huge shortage of addresses on the Internet, why would they do something crazy like that?"
The reason is that, when IPv4 was designed, they didn't realize that they were going to run out of addresses, so they thought, "Hey, it's no problem, we can assign 16 million addresses for testing, it doesn't matter, because we don't have a shortage of addresses."
Let me give you a demo of using the loopback. Let’s open the command prompt and enter the command ipconfig. You'll see that the IP address 127.0.0.1 is not assigned to any network card, it’s built-in IP.
So, I can ping 127.0.0.1, which is the loopback address, and you’ll see it getting replies which means it's up. The reason you do this loopback test is to test that the TCP/IP is working on the local machine.
Let’s say that you're in New York and you want to check that you've got connectivity to a server in Boston. You could ping that server but there's not much point in pinging a server in Boston if you can't get to your local default gateway router in New York, so you would ping that first.
Also, there's not much point in pinging the local router, if TCP/IP isn't even working on your laptop. So the way that you verify that TCP/IP is up and running on your computer is by pinging the loopback address.
It's the entire Class A range beginning with 127 that is reserved for testing loopback. I don't have to ping 127.0.0.1, I could ping 127.100.200.50 as well. I can ping anything beginning with 127 and it's going to check the local TCP/IP stack. It's good to have that address for testing, but not so good that they took out an entire Class A network for it.
Subnetting
A company that had a Class A address, would not put all 16 million hosts into a single logical network, that would be terrible for performance and security. They would split that big /8 range up into smaller subnetworks and assign those to their different departments in their different offices.
For example, if they received a Class A address 15.0.0.0 /8, they could allocate the subnet 15.0.1.0 /24 to sales computers in New York, 15.0.2.0 /24 to accounting, and 15.0.9.0 /24 to sales computers in Boston.
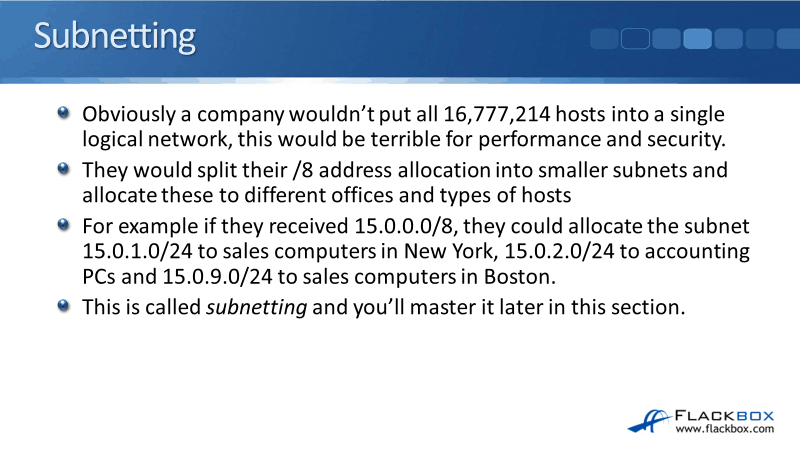
They would have that huge network that was assigned by the Internet authorities and they would split it into smaller subnets, this process is called subnetting. In this manner, they could assign them to their different types of hosts in different offices.
Class B
Class B addresses were originally assigned to medium to large-sized networks. With Class B, the first two bits in the address are always going to be set to 1 and 0.
Class B subnet mask default is /16, which is the first two octets. The network addresses range from 128.0.0.0 to 191.255.0.0 and it allows for 16,384 networks and 65,534 hosts on each of those networks.
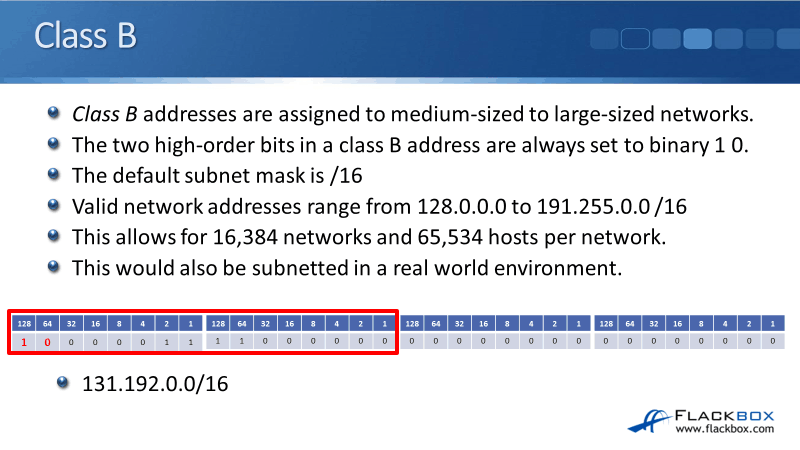
Again, you would never have a flat subnet with up to 65,000 hosts in there. If you were given a Class B network in the real world, you would subnet it into smaller subnetworks.
Class C
The last one that can be used to assign addresses to hosts is Class C and this is used for small networks. Class C has the default subnet mask of /24 which is up to the end of the third octet. With Class C, it's the first three bits that are important so they're always set to binary 1, 1, and 0.
The network addresses range from 192.0.0.0 to 223.255.255.0. That allows for a little over two million networks and 254 hosts per network.
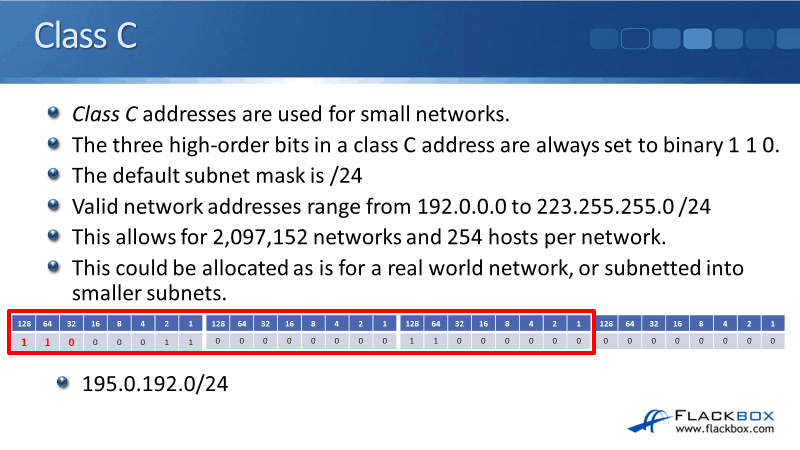
Class C is small enough that it could be allocated as-is for real-world deployment. But, we could subnet it into smaller networks as well.
A Quick Note on Private Addresses
I gave you all the addresses that were available in our Class A, B, and C networks. We spoke about the reserved addresses for our loopbacks and the addresses beginning with zero as well.
There's also a range of reserved private addresses in each class. Those are valid to be assigned to hosts, unlike the other reserved addresses, but the difference is that these are not routable on the public Internet. These were originally designed for hosts in a closed private network but they should have no Internet connectivity.
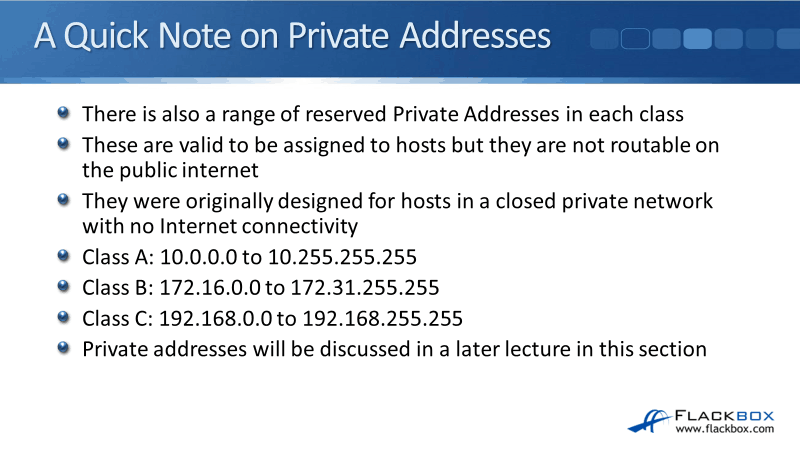
For example, in a high school, you've got students that need to work on PCs. However, you don't want them to be able to browse the Internet, so you would put them on private addresses.
The benefits that you get from that are:
- They can't get hacked because we're not connected to the Internet.
- It doesn't cost you anything. Unlike public IP addresses, private IP addresses are free.
The different ranges that are used for our private addresses are:
- Class A - 10.0.0.0 to 10.255.255.255
- Class B - 172.16.0.0 to 172.31.255.255
- Class C - 192.168.0.0 to 192.168.255.255
Address Classes
We discussed earlier that Classes A, B, and C include all the addresses that are valid to be assigned to our and hosts. Those address went up from 1.0.0.0 in the first octet, up to 223.255.255.255.
You may be thinking, "What about 224.0.0.0 to 255.255.255.255," because you know that the maximum value in each of our octets is 255, but we only went up to 223.
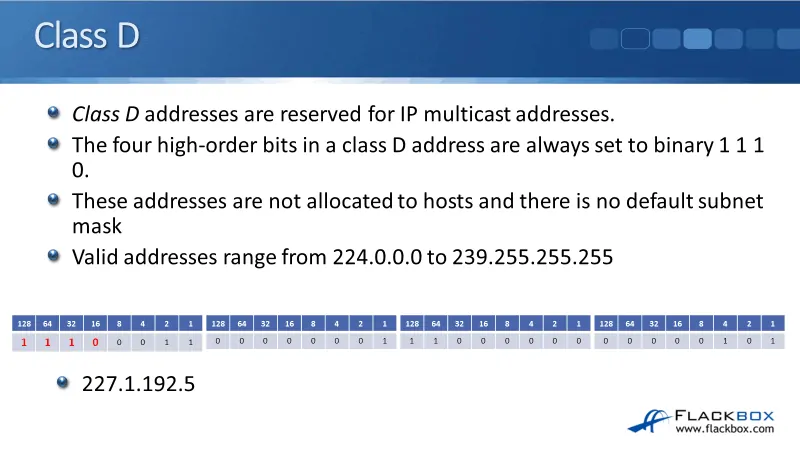
Class D
With Class D, the four high-order bits or the first four bits in the first octet are always set to the binary value of 1, 1, 1, and 0 as shown in the figure below.
If we add these up, 128 plus 64 plus 32 is equal to 224. So, the lowest address is going to be 224, then the remaining bits over to the right are 8, 4, 2, and 1 which adds up to 15. 224 plus 15 adds up to 239.
That's where we get the range of 224.0.0.0 to 239.255.255.255 from. These Class D addresses are not allocated to hosts and there's no default subnet mask. Class D addresses are used for multicast traffic.
Unicast Traffic
To see how multicast works, let's do a quick review of unicast first. In the example below, I've got my sender over on the left, which has a source IP address of 10.10.10.10. It is going to send traffic to destinations at 10.10.10.15 and 10.10.20.15.
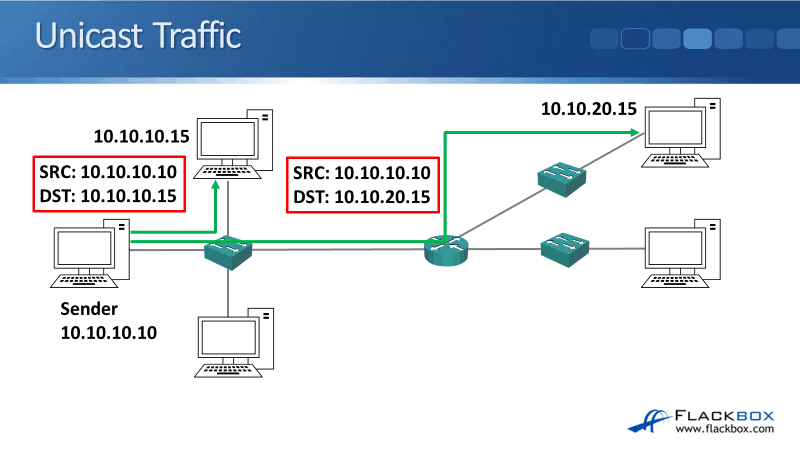
The sender sends traffic to 10.10.10.15 and if you look into the packet’s Layer 3 IP header, you would see that the source IP address is 10.10.10.10 and the destination is 10.10.10.15.
If we're using a /24 subnet mask, they would be both in the same subnet. Therefore, the traffic can go directly between the hosts without having to go via a router.
Then, the sender sends traffic to the other host up on the top right, 10.10.20.15. Let's say that this is a video stream that we're sending. We've unicast it to 10.10.10.15, so next, we unicast it to 10.10.20.15 as well.
If you look in the IP header again, the source address is 10.10.10.10, the destination address is 10.10.20.15. We were using the /24 subnet mask, so they're on different networks. The traffic needs to pass through via a router.
This was video streaming we were doing here, thus, it is two completely separate pieces of traffic. It is going to use 2 MB if it was 1 MB per stream. Now, we can improve this by using multicast traffic.
Multicast Traffic
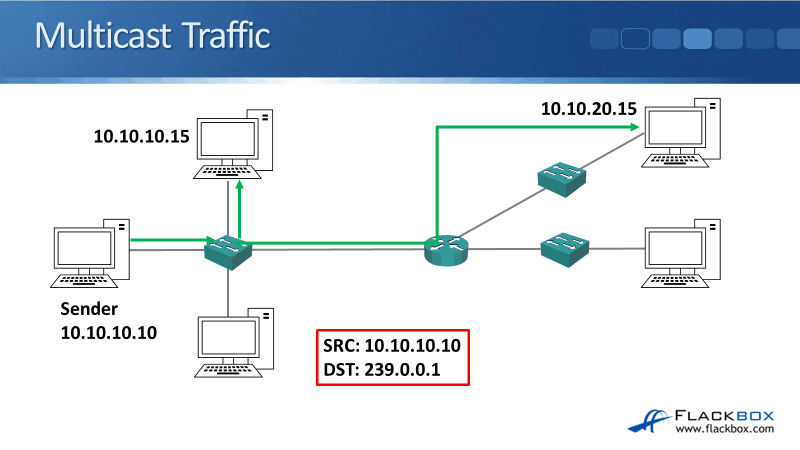
With multicast traffic, we're going to send one copy of the traffic from 10.10.10.10, and that one copy is going to be sent to 10.10.10.15 and 10.10.20.15. We're going to run an application on the sender which is going to send as multicast traffic. In our example, we're going to send it to our destination multicast address of 239.0.0.1.
It still comes from the same source address of 10.10.10.10 and the destinations still have their normal unicast addresses there as well. The difference is that we’re going to send it to this special multicast address. The traffic will then go to all of the hosts that are interested in getting the said traffic.
A good analogy of this is, you can think of it like tuning into a radio station. The hosts, 10.10.10.15 and 10.10.20.15, run an application that said that they wanted to receive the stream for 239.0.0.1. Now, as long as you've configured support for this on your routers, the traffic will get forwarded to all of the hosts that are interested in receiving it.
The benefit you get is, in our example, we're only sending 1 MB worth of bandwidth rather than 2 MB. If there were 50 interested hosts, it would still just be 1 MB worth of bandwidth rather than 50 MB. You would save a lot on the bandwidth, making things a lot more efficient.
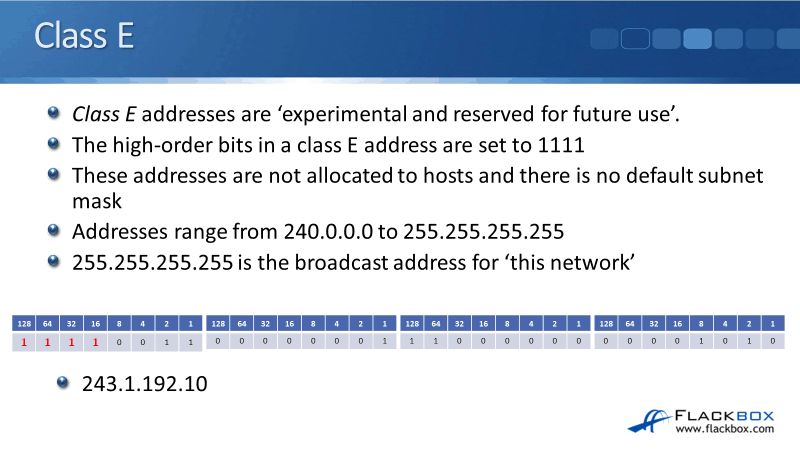
Class E
Class E addresses are experimental and reserved for future use. The first bits in Class E are always set to 1, 1, 1, and 1. If we count it up, that's going to give us possible values of 240.0.0.0 to 255.255.255.255.
Just like our Class D multicast addresses, these addresses do not have a default subnet mask. There is one special address that is used in Class E, which is the broadcast address of 255.255.255.255. That is the broadcast address for ‘this network’. Meaning, whatever network the source is on, it's a broadcast address for that network.
Using our previous example, I'll explain further why multicast is different and can be more efficient than broadcast traffic.
Notice in the example that on the local subnet, the hosts that are attached to the switch, it only went to the top host at 10.10.10.15, the traffic did not get sent down to the host below that at the bottom.
With broadcast traffic, it would be sent to all hosts on that subnet, not just the ones that wanted it. Multicast is more targeted and it's more efficient. Another difference is that as long as you've configured your routers to support it, routers will forward multicast traffic.
That's how we were able to get it to the host up in the top right. Broadcast traffic does not go outside its own local subnet and it does not get forwarded by routers by default.
Class E reserved addresses are never really used. You need to know what they are, particularly for the CCNA exam. In the real world, you'll never come across Class E addresses because they're not used in production environments. Class D addresses are used if you're using multicast.
IP Address Class Summary
Let's just have a look at a summary of the different classes:
Classes assigned to hosts:
- Class A – 1 to 162 /8
- Class B – 128 to 191 /16
- Class C – 192 to 223 /24
Reserved classes:
- Class D – 224 to 239 for Multicast
- Class E – 240 to 255 for Experiments
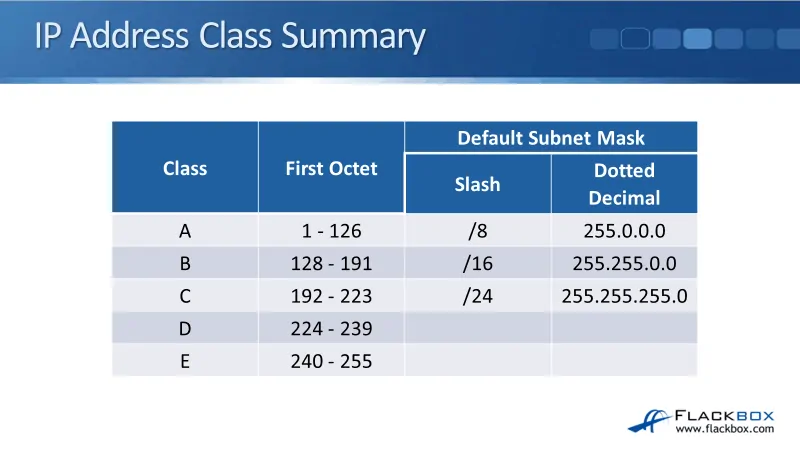
You want to have these classes committed to memory, not just for the CCNA exam where they're completely essential. They're completely essential for real-world networking as well.
Additional Resources
IP Addressing and Subnetting for New Users: https://www.cisco.com/c/en/us/support/docs/ip/routing-information-protocol-rip/13788-3.html
Chapter: Configuring IPv4 Addresses: https://www.cisco.com/c/en/us/td/docs/ios-xml/ios/ipaddr_ipv4/configuration/xe-3s/ipv4-xe-3s-book/configuring_ipv4_addresses.html
IANA Internet Protocol Addressing Systems: https://www.iana.org/numbers
Libby Teofilo

Text by Libby Teofilo, Technical Writer at www.flackbox.com
Libby’s passion for technology drives her to constantly learn and share her insights. When she’s not immersed in the tech world, she’s either lost in a good book with a cup of coffee or out exploring on her next adventure. Always curious, always inspired.